Tracking a blockchain transaction begins with a digitally signed message that encodes sender, recipient, amount, and fees. Each step depends on the network’s protocol, latency, and finality guarantees. Analysts weigh fork risks, confirmation timelines, and fee economics across consensus mechanisms. The process combines on-chain data with auxiliary signals, using graph analysis while considering privacy and data minimization. The methods are rigorous, yet ambiguities and hidden channels persist, inviting careful scrutiny to determine what can be inferred next.
What Happens When a Blockchain Transaction Is Created
When a blockchain transaction is created, a sender initiates a transfer by constructing a digitally signed message that encodes the transfer details (sender, recipient, amount, and fees) and binds it to the network’s protocol.
The process is methodical, skepticism accompanies assumptions about latency, and observers note fee economics, tracing how decisions affect tracking latency and overall system openness for freedom-minded participants.
How Transactions Get Confirmed on Different Blockchains
Transactions on different blockchains reach finality through varied consensus mechanisms, and understanding these mechanisms is essential to predict confirmation times and security guarantees. In practice, confirmations hinge on block generation rates, finality rules, and fork risks, with skepticism warranted about optimistic timing.
Privacy pitfalls emerge when cross-network visibility interacts with latency, while network latency remains a practical constraint on transactional throughput and perceived reliability.
Tools and Techniques to Trace Transaction Paths
Tracing the path of a transaction requires a disciplined approach that bridges observed on-chain data with auxiliary signals from network nodes and peers. Analysts employ graph analysis, clustering, and heuristic tracing while maintaining skepticism toward incomplete data. Tools emphasize Tracking privacy concerns and ensure auditability, yet every case reveals Forensics limits, because hidden mixers, off-chain channels, and evolving privacy techniques confound canonical path reconstruction.
Practical Troubleshooting and Privacy Considerations in Tracking
Practical troubleshooting in tracking blockchain transactions demands a disciplined approach: practitioners must anticipate noise, verify signals across multiple sources, and methodically document each decision. The detached observer notes frequent data ambiguities, reinforcing skepticism about alleged monotonic clarity. Privacy considerations emerge as privacy risks persist despite tooling, while data minimization guides are essential to limit exposure without compromising traceability. Freedom-seeking readers deserve precise, balanced procedures.
Frequently Asked Questions
How Do I Identify the Original Sender in a Coinbase Transaction?
In a coinbase transaction, the original sender cannot be identified; it is created by miners. The methodical view notes anonymity pitfalls, privacy considerations, and skeptical limits, emphasizing that freedom-seeking individuals should avoid assuming traceable origin reliability.
Can Transaction Tracing Reveal Exact User Identities on Public Chains?
Transaction tracing does not reveal exact user identities on public chains; ethics and anonymity are protected only by data minimization, cautious analysis, and skepticism about linkage capabilities, even as freedom-seeking observers pursue transparent, responsible insights.
What Are Common Mistakes Beginners Make When Analyzing Blockchain Data?
Mistakes hover like rusted anchors; common pitfalls derail insight. The analyst, skeptical and methodical, treats data interpretation as a delicate instrument, guarding against overinterpretation while pursuing clarity. Freedom-seeking readers deserve disciplined, evidence-based conclusions, not speculative certainty.
Do All Blockchains Support the Same Level of Traceability?
Blockchains do not universally support identical levels of traceability; transparency varies. From a blockchain basics perspective, some designs emphasize privacy considerations, while others trade openness for efficiency, enabling differing degrees of transaction visibility and user anonymity. Skepticism remains necessary.
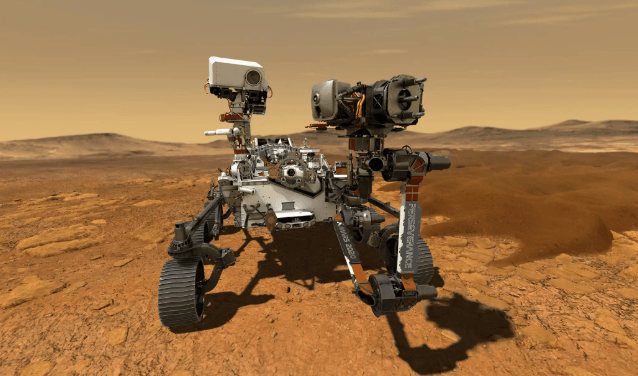
See also: Technology for Disaster Management
How Can I Stay Compliant With Privacy Laws During Tracking?
Like a cautious navigator, one ensures privacy compliance during tracking by prioritizing data minimization, evaluating metadata sensitivity, and assessing risk of re-identification, while skeptically documenting procedures and maintaining freedom-focused, methodical governance.
Conclusion
In the ledger’s quiet loom, each transaction is a seed threaded into a vast, stubborn tree. Leaves tremble with fees and time, yet roots cling to block timetables and forked vows. A skeptic’s gaze traces the lattice—addresses as coordinates, hashes as fingerprints, confirmations as weather. Trust, like sunlight through a canopy, arrives intermittently. The path is urged by incentives and dampened by opacity, until the forest reveals its pattern: disciplined signals, tempered by doubt, guiding cautious explorers onward.